Cybersecurity Consulting
How to Perform a Network Security Audit for Your Business
October 02, 2021
4 minutes

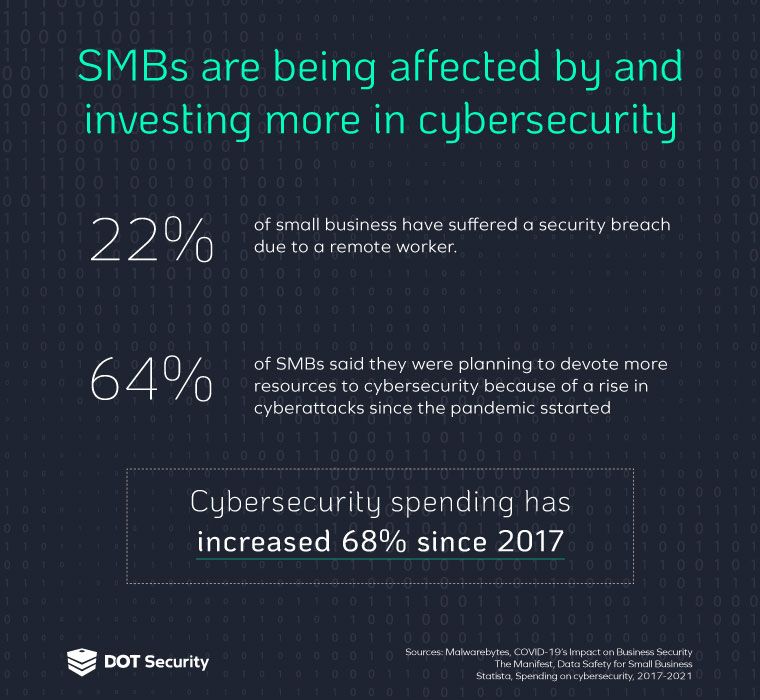
Due to the rising amount of cyberattacks throughout the last few years, and being accelerated thanks to the pandemic, many businesses who never considered their cyber safety are now having to look for their own vulnerabilities and what they can do to protect themselves.
Let’s examine if your business needs to assess its cybersecurity needs in the form of an audit and how you can use an audit to detect vulnerabilities in your network.
What is a Network Security Audit?
First, we’ll define what exactly a network security audit is.
The purpose of a network security audit is to establish two things which are absolutely crucial to building a strong cybersecurity strategy for your business: discovering your vulnerabilities and recognizing your risks.
Typically performed by a managed security service provider (MSSP), a network security audit can determine both vulnerabilities and risks through vulnerability scanning and penetration testing.
Sign up for our newsletter!
A network security audit performed by an MSSP can give you a breakdown of where your biggest vulnerabilities are and what solutions will help you mitigate them.
Do You Need a Network Security Audit?
Unfortunately, small to medium-sized businesses (SMBs) tend to neglect their cybersecurity, wrongly thinking that they aren’t at risk due to their size or thinking that their old, more rudimentary defenses like anti-virus software are enough to stop the threats of today.
SMBs are often targeted because of these very reasons. 43% of all cyberattacks are targeted at SMBs who are unprepared to prevent these attacks or react appropriately after they occur.
With more complicated cyberattacks and more complicated business than ever, it’s important that you learn your business’ unique cybersecurity needs through a full network security audit.
What Happens if My Network is Breached?
The reason you want to be protected from attacks and able to quickly and appropriately react if you are attacked is because the cost of a cyberattack is often devastating for a business.
The average cost of a data breach is $4.45 million. 93% of businesses who suffer a major data breach go out of business within a year.
In addition to the financial cost, your reputation also takes a massive hit as consumers will wonder how seriously you’re taking data security, especially in industries like finance and health when you’ll have to handle private, sensitive information and adhere to strict data protection laws and regulations like HIPAA
How to Perform a Network Security Audit
If you do not have your own internal IT team, similar to most SMBs, then it may not be feasible for you to perform your own network security audit.
Paying for a full cybersecurity team is too expensive for most SMBs because these teams are usually made up of multiple people in various roles, such as:
- Cybersecurity Analysts (CSA)—Executes assessment tasks, analyzes data, performs daily monitoring tasks.
- Cybersecurity Engineers (CSE)—Prepares final assessment of cybersecurity solution strategy implementation.
- Cybersecurity Developer (CSD)—Develops and maintains IT security assessment and pricing tools and works with organizations to improve and automate processes.
- Compliance Managers—Develops solutions and strategies based on achieving compliance into managed IT security strategy.
This is why many businesses choose to work with an MSSP, instead. A managed security service provider has the tools, expertise, manpower, and bandwidth needed to perform a truly complete network security audit.
Not only that, but an MSSP will even recommend programs and tools that are specifically chosen to help your business and solve your network security issues.
What Makes Up a Modern Cybersecurity Solution?
Cyberattacks continue to evolve and become more complicated by the day. In order to combat modern cyberattacks you must have a modern cybersecurity strategy.
Here are some of the most important components of a cybersecurity strategy that will help your business stay safe among the ever-changing landscape of cyberattacks.
- Perimeter Security: Commonly referred to as a firewall, perimeter security acts as the shield between your network and the outside internet. Aside from a firewall, this comes in many different forms, including antivirus software, intrusion detection, spam filtering, and VPN support.
- Endpoint Protection: This form of defense prevents devices connected to your network from becoming compromised and potentially letting attackers gain access to your systems.
- Information Security: This prevents data loss due to inadvertent circumstances by determining who has access to certain information, where it’s stored, and where it can be shared.
- Authentication Protocols: This ensures that whoever is accessing your business data is who they say they are. It helps to prevent unauthorized access to private information.
- Backup and Disaster Recovery: This makes sure that you can retrieve any lost data in the event of a breach to help your business fully recover.
- Monitoring: This allows your IT team (internal or MSSP) to monitor your network and keep an eye out for signs of suspicious activity.

Deciding if you need a full network security audit really comes down to how much you’ve dedicated and invested into cybersecurity in the past and how much of a sense you have of your current defenses in place. Do you need the components listed above? Do you already have some of them?
If you’re unsure, a network security audit will help you learn where your biggest risks and vulnerabilities are and which solutions you’ll need to shore up your defenses in order to address them. The exact answer varies by business depending on size, workforce, industry, and other factors.
But, no matter the business, the best way to obtain a true understanding of your cybersecurity needs is by investing in a network security audit.
Ready to learn more about cybersecurity and considering a risk audit? Contact DOT Security to speak with an expert today.
