Cybersecurity Consulting
The DOT Security Risk Audit
July 11, 2024
7 minute read

Whether you’re starting a new business and want to prioritize cybersecurity from the get-go, or if you’re just looking to evolve your cybersecurity strategy, the process is going to start with a risk audit. Through the audit, cybersecurity experts get to know the nooks and crannies of your environment, see your vulnerabilities, and build out a plan for custom security solutions that provide comprehensive coverage.
If you’ve never undergone a cybersecurity risk audit before, though, it can be nerve-wracking to allow external users into your network, especially white-hat hackers, if you don't know exactly what it entails.
Sign up for our newsletter !
So below we take a deep dive into every step of the DOT Security Risk Audit, to answer all of your questions about what a cybersecurity risk audit is, how it helps your business, and some of the insights that you’ll take away from the process.
If you want to see how your current cybersecurity strategy measures up to industry standards and best practices, take a few minutes and review DOT Security’s Cybersecurity Checklist: How Covered Is Your Business?
Why DOT Security Always Starts with a Cybersecurity Risk Audit
Starting your security journey with a cybersecurity risk audit is essential because it provides a foundational understanding of an organization's current security posture and identifies potential vulnerabilities. This systematic evaluation uncovers weaknesses that could be exploited by cyber threats, allowing organizations to prioritize resources and efforts on areas posing the greatest risk.
This ensures that time and money are spent effectively on critical aspects of security.
Moreover, a cybersecurity risk audit helps align security measures with the organization's overall business objectives. By understanding specific risks, stakeholders can make informed decisions to protect valuable assets like customer data and intellectual property.
This alignment creates a balanced approach, safeguarding the business without hindering its operations and growth. Additionally, conducting a cybersecurity risk audit early fosters a proactive security culture within the organization. It raises awareness among employees about potential threats and the importance of adhering to security protocols.
Identifying and addressing risks early allows for the implementation of training and policies that mitigate these risks, enhancing overall security and ensuring compliance with relevant regulations and standards, thereby protecting the organization from legal repercussions and building trust with customers and partners.
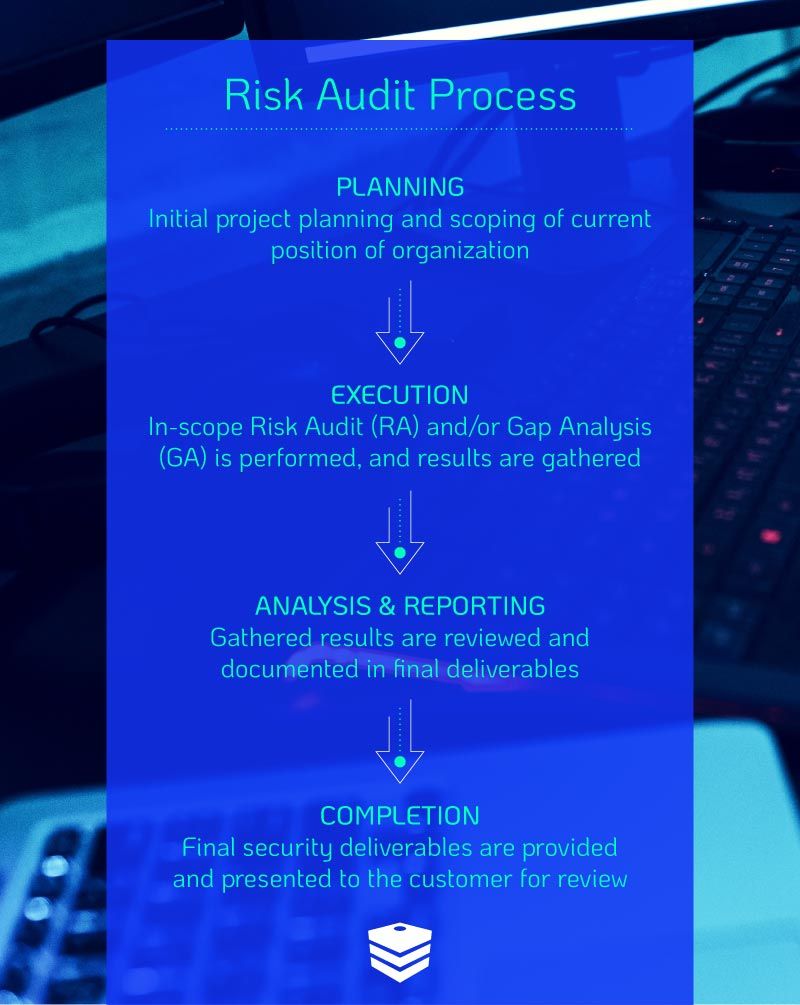
1. Creating a Plan
Developing a plan is the initial stage of a cybersecurity risk audit and is a critical step in the process. This phase involves defining the scope and objectives of the audit, which includes determining what systems, networks, and data will be assessed. It is essential to gather input from key stakeholders to understand their concerns and priorities, ensuring that the audit addresses the most critical areas.
A thorough understanding of the organization's business processes, assets, and the potential impact of cyber threats is crucial. The planning stage also involves identifying the resources required, such as personnel, tools, and technologies, and establishing a timeline for the audit. This includes selecting the right team members with the necessary expertise and ensuring they have access to the tools needed for an effective assessment.
The risk criteria and the framework to be used for the audit should be defined at this stage, whether based on industry standards such as NIST, ISO/IEC 27001, or other relevant guidelines. Detailed planning ensures that the audit is comprehensive and efficient, setting a clear path for execution. Additionally, this stage involves establishing communication protocols to keep all stakeholders informed and engaged throughout the audit process.
This meticulous preparation helps in anticipating potential challenges and developing strategies to address them, thus laying a solid foundation for a successful audit.
2. Executing the Plan
Execution is the stage where the actual assessment of the organization's cybersecurity posture takes place. This involves a comprehensive examination of information systems, networks, applications, and security policies. The execution phase typically includes vulnerability scanning, penetration testing, and reviewing access controls and configurations.
These activities help identify weaknesses that could be exploited by cyber threats. Auditors collect data through interviews with key personnel, system logs, configuration files, and direct observation. It is crucial to follow the predefined plan closely while remaining flexible to address any unforeseen issues. Detailed checklists and methodologies are often employed to ensure no critical areas are overlooked.
Auditors might also simulate real-world attack scenarios to test the resilience of the organization's defenses. This stage provides the raw data and insights needed to identify vulnerabilities and assess the effectiveness of current security measures. Regular communication with stakeholders during this phase is essential to provide updates and address any immediate concerns.
This hands-on investigation is the core of the audit process, generating the evidence needed for a thorough analysis in the subsequent stage.
Vulnerability Scanning
When a cybercriminal decides to target your business, the first thing they will do is search for the easiest weakness in your network to exploit. So that’s the first thing DOT Security does during a cybersecurity risk audit, too.
Attackers never want to do more work than necessary, so they’ll take the path of least resistance into your system. Anything we find during vulnerability scanning will be among their most likely access points.
Entry points that would allow a bad actor to move laterally through your system once they’re in are of particular interest at this stage of the process, as those will be the most important ones to cover later. In short, vulnerability testing is where we map out your entire network and figure out exactly what avenues of attack a hacker would use to gain access to it.
Penetration Testing
This is the part of the cybersecurity risk audit where a hacker gets into your system on purpose.
A member of DOT Security’s white-hat team, using the tactics of a cybercriminal attempting to get into your network, will figure out how they could do it, further clarifying where your biggest weaknesses are and what needs addressing.
White hat hackers are security professionals who understand and can mimic the way attackers work but use that information to make recommendations as to how to help keep your business safe.
They conclude testing by reporting on all of their findings. Penetration testing is always performed ethically and is a vital part of the process. Having white hat hackers work on your system is extremely valuable for risk assessment. It shows how a malicious hacker would behave, and the methods they would use to access your data.
Gap Analysis
The gap analysis is a process for discovering if an organization’s cybersecurity and business practices meet their industry or location’s standards.
DOT Security’s Compliance Officers primarily focus on data handling and safeguarding, as well as how well legal policies are being enforced. With this understanding, a business can see if they’re compliant with any relevant regulations, and what they would need to do to become so if they aren’t.
Some industries, like healthcare, education, and finance, are heavily regulated by local and national governments, requiring them to follow a series of laws focused on data security, like HIPAA.
However, even if your company isn’t in one of those industries, it still might be worth considering a gap analysis as part of your cybersecurity risk audit to ensure that you meet new or soon-to-come universal standards, like the CCPA in California, the SHIELD Act in New York, or the GDPR, which affects any company with users in the EU, regardless of where the company is based—same for CCPA and SHIELD.
By investing in data security and compliance early, and preparing your business for stricter regulations, you’re more likely to be ready as more such laws come to pass. Plus, you’ll have a more secure service for your customers, which is an increasingly important aspect of data privacy on which businesses are competing today.
3. Analysis and Reporting
The final step of a cybersecurity risk audit is the simplest, but also the most actionable. DOT Security will come back to all of the key stakeholders identified at the beginning and report on our findings. We break down every aspect of our assessment, from your vulnerabilities and weaknesses to what your organization needs, both from a cybersecurity and a business perspective.
If you opted for a gap analysis, this is also where we present our findings on your compliance. This all includes our findings, any specific observations we’ve made, if there are glaring holes that require immediate fixing, and our long-term recommendations.
Using this data, DOT Security will then work with you to create a security plan that addresses the issues we’ve found and is customized specifically for your business.
Wrapping Up on the DOT Security Risk Audit
Now you know what a cybersecurity risk audit from DOT Security involves, how our cybersecurity professionals behave when performing one, what you will receive from it, and how it can help you move forward.
Risk audits are a critical first step in any security plan. There’s no better way to figure out where your system stands now, and how to get it to where it needs to be. Plus, as cybercrime becomes more sophisticated, it is more important than ever to conduct regular security audits to look for gaps in and continually improve your security positioning.
Review DOT Security’s Cybersecurity Checklist: How Covered Is Your Business? To get an idea of how complete your current cybersecurity strategy is and where there’s room for improvement!
