Identity And Access Management
[Guest Post] What is Passwordless Authentication?
January 04, 2024
7 minute read

Contributed to by David Konstant, Associate Cybersecurity Engineer, DOT Security
Hackers love passwords. This may sound like a bold statement, but it’s true. Some passwords are more loved than others. Short passwords, ones with common and easy to guess words, and ones that lack complexity are favorites.
But even great passwords or passphrases can be leveraged by hackers if they are disclosed because of a data breach or a social engineering campaign like a phishing attack.
Sign up for our newsletter!
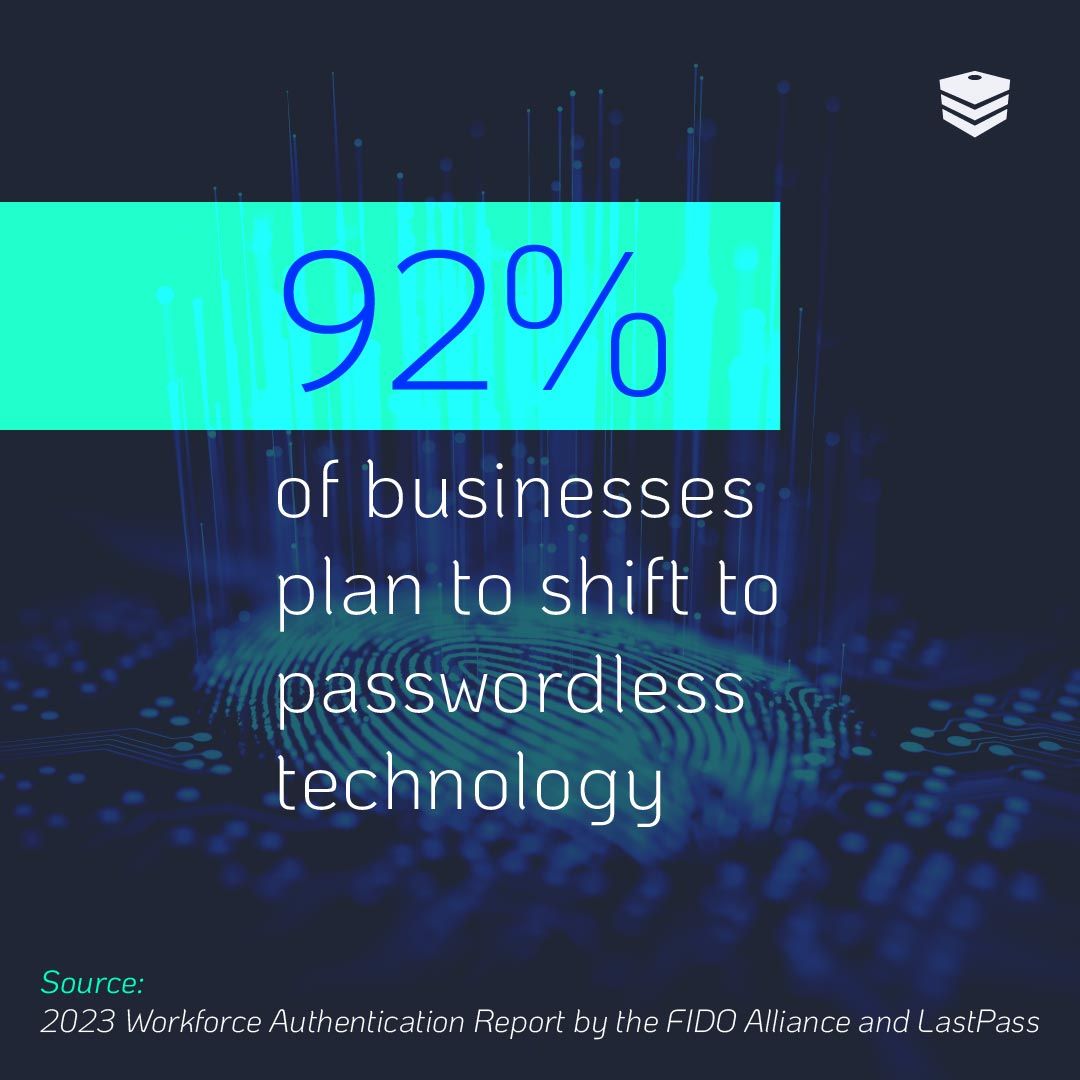
Passwords have long been the main authentication method for computers, but with emerging technologies and the proliferation of smartphones, there is a lot of buzz about the concept of passwordless authentication and its merits in cybersecurity.
Passwordless authentication is a great way to protect your business. Ensure your business hasn't overlooked other cybersecurity protocols by assessing DOT Security's Cybersecurity Checklist, How Covered is Your Business?
What is Passwordless Authentication?
Passwordless authentication, as the name suggests, replaces passwords with other authentication methods to add an additional layer of security. Authentication is the process of determining that someone is who they say they are. This process is closely tied to identification, the process of declaring who someone is.
Traditionally in authentication and identification, a user supplies a username as their identity and a password for authentication.
Passwordless authentication solutions aim to eliminate the vulnerabilities around managing passwords completely.

How Does Passwordless Authentication Work?
Passwordless authentication works by replacing the traditional authentication method to which digital users are accustomed: the password. Instead, it makes use of non-reproduceable assets.
For example, biometrics are a common way modern tech is approaching security. Using someone’s thumbprint or facial recognition as the authenticator means malicious users can’t steal credentials over the internet.
The theory behind adopting a passwordless culture is that it limits how many vulnerable points of access malicious users have to attack. By limiting the attack surface area, you can greatly reduce the risk of a successful attack. However, certain passwordless systems can create a single point of failure, which is discussed in further detail later on.
Let’s delve into the passwordless authentication practices you should consider implementing in your organization.
Passwordless Authentication Solutions
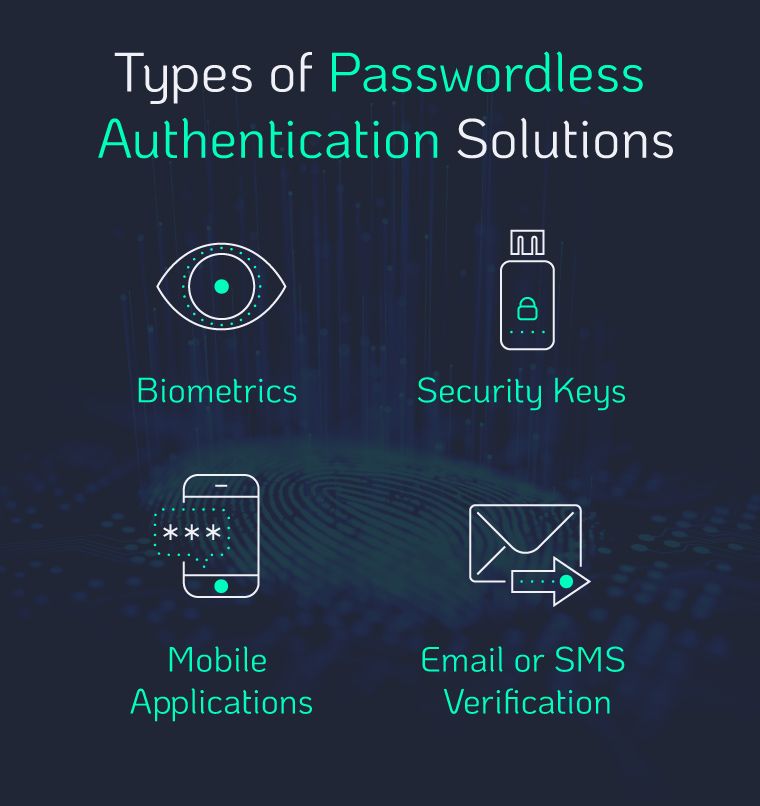
There are a wide variety of passwordless authentication solutions to consider. Understanding the differences between these solutions will help you determine if integrating a passwordless system makes sense for your security needs.
Some of these passwordless authentications are simply an additional step using something you know through a mobile device application, SMS, or e-mail that provides a one-time code or button. This is similar to having a multi-factor authentication (MFA) policy in place.
But some take advantage of new innovations in business technology to elevate security to another level by making use of something you have—referring to a physical key of sorts, oftentimes a USB—or something you are—like biometrics which are unique to you.
A couple of these passwordless authentication technologies include:
-
Biometric Authentication: Biometrics, like facial recognition and fingerprint readers, are significantly more secure than traditional passwords but are not always available on computers. Biometric authentication relies on a unique characteristic of an individual, or “something you are” like facial features, fingerprints, etc.
-
Security Keys: Another common passwordless authentication technology is security keys. These devices are “something you have.” They are physical devices that need to be connected to perform authentication without the user putting in a password. These are usually USB devices that are physically plugged in but can also use NFC or Bluetooth to connect.
-
Token-Based Authentication: This technology allows users to input their credentials once and receive a unique encrypted string of random characters in return. This token can then be utilized to access protected systems, eliminating the need to re-enter credentials. The digital token serves as proof of existing access permission.
-
Certificate-Based Authentication: Certificate-based authentication uses digital certificates— electronic documents comparable to IDs—to verify a user's identity with a public key and the certification authority's digital signature, proving key ownership and exclusive issuance.
Multi-Factor vs. Passwordless Authentication
Multi-factor authentication (MFA), a digital identity verification system requiring users to pass multiple authentication checkpoints, is similar to passwordless authentication because it can includes some of the same determinants, like biometric factors, but still also uses usernames and passwords.
Passwordless authentication may sound very similar to MFA, but MFA uses passwordless authentication methods to add extra authentication factors along with a password for an extra layer of defense.
With MFA, you log in with your username and password and then are prompted to enter additional information, such as a one-time access code sent to an authenticator app on your phone. MFA acts as an additional layer of protection for your accounts because hackers would have to not only know your password but also have access to your phone to log into your accounts.
Systems configured with MFA may ask for a one-time access code, a fingerprint, or a link sent to your email to verify that the person logging into your account is, in fact, you.
Benefits of Using Passwordless Authentication
Now that we’ve looked at how passwordless authentication works, we can delve into the various benefits that stem from committing to a passwordless culture.
Below are several compelling reasons to introduce passwordless authentication:
-
Simplified Account Management: Passwordless authentication streamlines account management by removing the necessity for password resets and the challenges of account recovery. Additionally, it offers centralized authentication systems, enhancing the ease of managing and securing online accounts.
-
Improved User Experience: This is important because when passwords become a burden, users tend to start reusing the same passwords or find other shortcuts that lead to the types of bad passwords that hackers love.
-
More Difficult for Hackers to Compromise: It’s significantly harder to get a fingerprint over the internet than it is to get a password. Again, this is an example of passwordless authentication limiting the overall attack surface area available on the internet.
The benefits of passwordless authentication can extend to IT administration as well by decreasing the amount of time spent on password resets, as this is one of the most common support desk tickets.
Potential Drawbacks of Passwordless Authentication
Passwordless authentication is not perfect. USB security keys are subject to theft, one-time codes sent via email and SMS can still be targeted by social engineering attacks, and some fingerprint readers have been bypassed by security researchers.
While passwordless authentication has many benefits, it can also be a single point of failure, either allowing for complete compromise or frustration for users. This is probably the biggest deterrent we see in the cybersecurity space when discussing passwordless authentication solutions.
Closing the Door on Passwordless Authentication
While passwordless authentication offers a lot of benefits, it is not for every organization. It is important to consider your organization’s state of authentication. The implementation process can be complicated when using legacy software and protocols. Companies should consider what devices users have access to and the cost to update or replace technology.
Companies that already leverage single sign-on for cloud applications and integrated authentication flows for on-premises equipment are better prepared for implementation and can benefit more rapidly.
Instead of ditching passwords, passwordless authentication methods should be considered by organizations as part of their MFA procedures as many are not ready for a full passwordless deployment. For other organizations, providing a fully passwordless system with multi-factor authentication, like using biometrics with security keys, might be possible.
Make sure your business isn’t missing any cybersecurity protocols. Review DOT Security’s cybersecurity checklist, How Covered Is Your Business?, to find out.
