Network Security Monitoring
Passive Threats: What You Need to Know
January 11, 2024
5 minutes

An Ohio public utility employee deployed a passive threat inside his company when he began recording the keystrokes in coworkers’ devices. He gained access to credentials and messages.
But what, exactly, is a passive threat? And how harmful are they to most organizations?
Sign up for our newsletter!
Read on to learn more about what a passive threat is, its goals, and what businesses can do to protect themselves from these often unseen and unknown cyberattacks.
To review your cybersecurity posture, download DOT Security’s Cybersecurity Checklist: How Covered is Your Business and see whether you have strong layers of protection.
What Is a Passive Attack?
A passive threat, also known as a passive attack, monitors a network to collect information and find vulnerabilities that can be used in a later attack.
The purpose of a passive attack is to gain sensitive data such as employees’ or customers’ personal details, a business’ proprietary files, information protected by regulations, etc.

Hackers also deploy passive attacks to gather user credentials and learn about the inner workings and weaknesses in a network environment.
Passive attacks are almost always reconnaissance-based and don’t involve direct action against a network, which is why they are difficult to detect.
These attacks have no direct effect on the system—until the information gathered is later used in an active attack. If a passive attack is spotted, then the hacker has failed in remaining undetected.
What’s the Difference Between Active and Passive Security Threats?
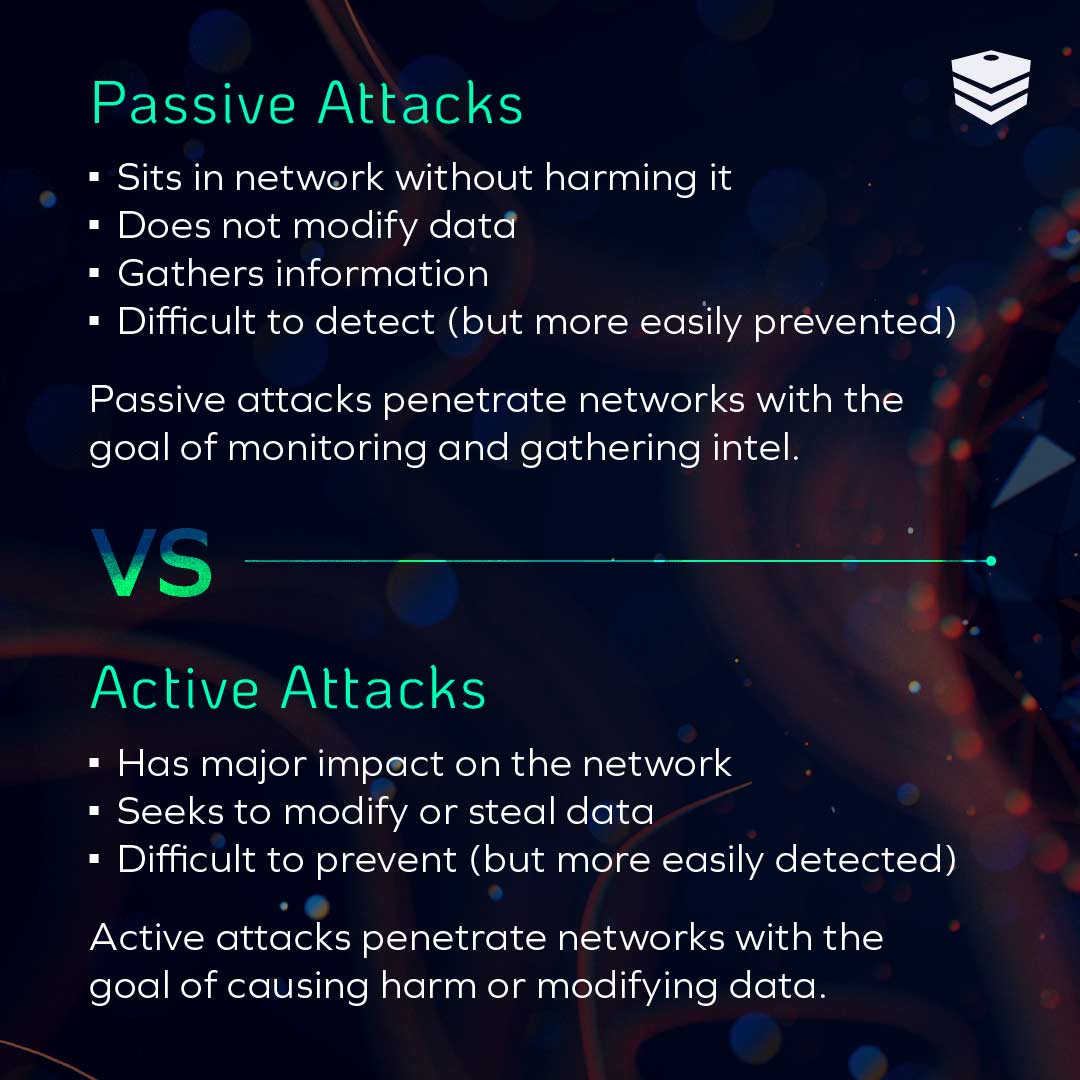
The main difference between active and passive threats is that an active attack attempts to modify a system’s resources or operations, while passive ones serve to gather intel.
Active attacks can make use of the information gathered during a passive attack. The aim of a hacker performing an active attack is to corrupt data or harm the system.
A passive attack focuses on collecting information without modifying anything within the system.
Think of passive attacks as the surveillance stage of a heist. The robbers collect information on their target location, the people working there, the hours of operation, etc. An active attack would be akin to the execution stage of a heist when the thieves use their knowledge to enter a site and steal the target items.
Other differences between passive and active attacks include duration and how easy they are to detect. Passive attacks last longer. Bad actors gathering as much intel as possible are harder to detect, since there is no immediate indication of data corruption.
Active attacks, on the other hand, are quicker in duration and are easier to spot since files are corrupted or systems harmed.
How Can Passive Threats Affect Your Network Security?
Though they don’t aim to destroy everything and bring down entire systems, passive attacks can still be highly detrimental to businesses that can’t find them and stop them with proper network security.
For the most part, a passive attack gets information by monitoring outgoing and incoming messaging or by tracking keystrokes to harvest passwords and other information.
Once they have this information, bad actors can sell that data to someone with more nefarious plans, or they can use it to plan future attacks.
An unnoticed passive attack can sit in a network for as long as it wants to, gathering more and more private and classified information from businesses, their customers, and their employees.
Types of Passive Attacks
Passive threats come in a few different forms depending on the attack’s goal. Here are a few of the most common passive threats that can harm a network:
-
Traffic Analysis Attacks: Traffic analysis attacks monitor and record network traffic as it moves between targeted systems. These attacks identify patterns of communication over a network to understand the identities of users and machines, their locations, and possibly the types of encryptions used on the data.
-
Release of Message Attacks: Release of message attacks monitor unprotected communications—such as emails, phone calls, or instant messages—to discover sensitive or classified information.
-
Footprinting Attacks: Footprinting attacks aim to gather as much information as possible from the target network’s hardware, software, employees, and customers. Information like IP addresses, domain name system information, employee IDs, payment information, and more are up for grabs.
-
Eavesdropping Attacks: Eavesdropping attacks listen in on private phone calls or unencrypted messages to capture sensitive information from conversations.
-
Installation of Keyloggers: Keyloggers are activity-monitoring software or hardware that can track and record a users’ keyboard strokes. Cybercriminals use keyloggers to record the credentials when a user types them. These credentials can then be used to access private accounts and escalate privileges.
How to Prevent Active and Passive Attacks
To prevent active and passive attacks, businesses must have the ability to identify and remediate these threats through dedicated cybersecurity monitoring services, updated software, and a layered cybersecurity strategy.
Old technology such as a “set it and forget it” antivirus won’t be enough when facing sophisticated attacks from modern cybercriminals.
Here are a few things businesses can do to protect themselves:
-
Use Next-Gen Antivirus Software: Next-gen antivirus software uses behavior algorithms that examine processes, data, application use, network activity, and user behavior to spot unusual activity that points to threats like passive attacks.
-
Encrypt Data: Encrypting data is a cybersecurity technique that helps to protect data from everyone but the intended recipient who holds the key. If intercepted by an unintentional party, the information will look incomprehensible. Encrypting data is a necessary step toward preventing breaches, especially during data storage and transfer.
-
Benefit from Specialized Persistence Detection: Persistence detection uses a team of cybersecurity professionals who monitor for any anomalies in your network. When software might not be able to identify a malicious file disguised as a regular file, human threat hunters can.
-
Have a Dedicated Cybersecurity Team: Having a dedicated team of cybersecurity experts to update your software, train your staff, and manage your overall security procedures is crucial for businesses that wish to minimize any cyber threat.
Takeaways
- Passive threats use monitoring tools to gather information on a network’s vulnerabilities without directly altering or damaging it. They are hard to detect because they make such little noise and focus more on reconnaissance and information-gathering.
- Although passive attacks don’t cause immediate system damage, they can still be highly detrimental by gathering sensitive information like login credentials, personal details, or proprietary data. If undetected, these attacks can persist in a network, accumulating more data over time which can be used in an active attack.
- Passive threats come in various forms, including traffic analysis, the release of message attacks, footprinting, eavesdropping, and the installation of keyloggers. Each targets different aspects of a network to gather information.
- Businesses need robust cybersecurity measures to combat passive attacks. Next-gen antivirus software, encryption, specialized persistence detection, and a dedicated cybersecurity team are crucial in identifying and removing these threats.
Bottom Line
A passive threat to a business’ network often lays low and works in the background. If you don’t have proper cybersecurity measures in place, they can go completely unnoticed for long periods of time, skimming information and monitoring activity for months or even years.
Make sure you have effective antivirus software, encryption, and an experienced cybersecurity team behind you to put your business in a good position to find, eliminate, and recover from potential passive attacks.
To find out if your network can withstand a passive attack, head over to our Cybersecurity Checklist: How Covered is Your Business? and review your cybersecurity strategy.
